C/Windows/System32/Shutdown.Exe ?
C/Windows/System32/Shutdown.Exe ?
Bad Rabbit The Full Research Investigation. What is this all about Earlier this week a new ransomware attack dubbed Bad Rabbit broke out and has so far affected The Ukraine, Russia, Turkey and Bulgaria. Various healthcare, media, software and distribution companies and critical infrastructure, such as the Ukranian train services, Odessa airport and The Ukranian Ministries of Finance and Infrastructure all suffered down time. What is the initial infection vector A drive by download type of attack, delivered mainly via popular Russian media sites, infects victims by tempting them to accept a fake Adobe Flash update. This is not a case of malvertising as our research indicates the tracker is embedded into the site code itself. Although the attack site is currently down, below is a partial list of the trackers that we can still see as active. Is there a lateral movement activity It is important to note that there is no presence of the Eternal. Blue exploit used in previous ransomware attacks. In windows 7 when you click start. Understand how this virus or malware spreads and how its payloads affects your computer. Protect against this threat, identify symptoms, and clean up or. Relic Of War Hacked Premium on this page. However, there is evidence of Bad Rabbit using mimikatz tools to move across the network via SMB open shares. Is this attack connected to Petya or Not. Petya No. There is so far no connection between Petya or Not. Petya as this attack is built on entirely new code base. Clock Software For Xp here. Please see below for a full flow of how Bad Rabbit operates. Technical overview. The malware consists of the following modules Module. Name. Details. Dropper. C windowsinfpub. 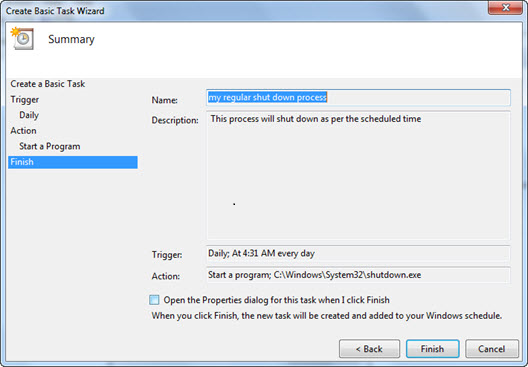 Credentials grabber, 3. C windows. tmpmimikatz based tool. Credentials grabber, 6. C windows tmpmimikatz based tool. Main payload. C windowsdispci. Driver, 3. 2bit. C windowscscc. Legitimate signed file dcrypt. Driver, 6. 4bit. C windowscscc. Legitimate signed file dcrypt. Landscape 20050901 shutdown. Windows. The diagram below represents the overall malware flow of execution. An interactive version of this diagram can be found here. The following contains a detailed technical explanation of each of Bad Rabbit module. Dropper. The Dropper module starts its execution by unpacking and running embedded an executable, which is run via rundll. The purpose of this unpacked DLL is to perform some preparatory actions before executing the main payload and setting up the driver. Once executed, it initially checks if the directory c Windowscscc. If not then the process is terminated. It then chooses the appropriate driver from within its embedded resource 3. The driver is executed via the service manager at the time of booting. The main payload executable is then written to C windowsdispci. Following a creation of a scheduled task named rhaegal which is used to execute it on every system restart using this command line schtasks Create RU SYSTEM SC ONSTART TN rhaegal TR C WINDOWSsystem. Windows 10, like its predecessors, offers multiple ways to access shut down, restart, hibernate and sleep options in Windows 10. You can access shut down o. What is this all about Earlier this week a new ransomware attack dubbed Bad Rabbit broke out and has so far affected The Ukraine, Russia, Turkey and Bulgaria. Share Threat Hunting Services Are Now a Basic Necessity on Twitter Share Threat Hunting Services Are Now a Basic Necessity on Facebook Share Threat Hunting Services. Windows 7. Windows Server 2008 R2 Thread, GPP Deploying Scheduled Tasks SOLVED in Technical Ok so Im trying to deploy a scheduled task but having some difficulty. Files-In-System32_cmd.png' alt='C/Windows/System32/Shutdown.Exe ?' title='C/Windows/System32/Shutdown.Exe ?' />In this video I will show you how to add the shutdown, restart, sleep and logoff buttons to the taskbar. Below are the codes you will use to make the. How to Automatically Shut Down Your Computer at a Specified Time. Do you always forget to switch off your computer before going to bed, or just forget to look at the. C Start C Windowsdispci. The id argument in the above command line is set with randomly generated 4 bytes. Following the dropper module, it schedules a system shutdown by creating yet another scheduled task named drogon by using this command line. Create SC once TN drogon RU SYSTEM TR C WINDOWSsystem. ST hh mm ss. It also deletes windows events and the USN drive c journal by using this command line. Setup wevtutil cl System wevtutil cl Security wevtutil cl Application fsutil usn deletejournal D c Once these actions are complete, the dropper deletes the drogon scheduled task and starts a separate thread in order to encrypt each of the system drives. Finally, a file named Readme. A public RSA 2. 04. This keys value is E5 C9 4. B9 5. 1 6. B E6 C4 3. E7 DE 4. 2 5. 5 6. F 6. 5C1 0. A D2 4. Qual O Melhor Site Para Baixar Jogos De Xbox 360 on this page. E 2. E 0. 9 2. 1 7. A 4. 3 A4 1. 7 D0 3. B5 1. E8. E FF 1. D F3 DF CF 5. 6 1. A 3. 0 BE ED 9. 3 7. C 1. 4 D1. B2 7. 0 6. C F3 7. 8 5. C 1. F 2. 1 8. C 6. D 9. E4 5. E 4. 3 C5. 71 6. B 1. A 5. 3 A9 5. B 1. 1 E2 5. 3 A6 E4 A0 7. B C6. A9 E1 3. 8 A7 1. B F1 8. D FD 2. 5 4. D 0. 4 5. C 2. 5 9. FB D1 5. 8 D9 8. A 8. A2 1. D 4. 4 EB E4 1. F 1. C 8. 0 2. EE2 7. E0 9. 9 9. 4 8. A 1. A 2. 7 9. B 4. 1 D1 8. C 4. 1C4 C9 1. B 0. B 7. 2 7. B 5. 9 6. C7 7. 0 1. F 5. 3 FE 3. E2. 36 0. D 8. C 1. F 9. 9 5. 9 F5 B1 0. E 9. 3 B6 1. 3 3. FC 1. 5 2. 8DA AD 1. D A5 F4 2. C 9. 3 B2 0. C 7. 8 3. 5 1. D 0. C E1. 4B 0. D 0. 3 8. D 5. B D3 8. E 8. A4 4. 7 1. D D5 EC F0 B7. F 4. 7 1. E 1. C A2 2. F 2. 6 C3 9. 6 D6 5. D 6. 6 3. 6DC 0. B EC A5 FE EE 4. CD 7. B 4. 0 9. E 7. C 1. C 8. 4 5. 9 F4. B7 5. B 5. B 9. 2 F8 DD 7. FD B1 0. 6 7. 3 E3 6. F 7. 1 8. 4D4 6. 0 3. F A0 6. 7 0. 6 8. E B5 DC EB 0. 5 7. C 5. 8 AB 1. F 6. File extensions to be encrypted. Bad. Rabbit can perform both encryption and decryption of the MBR and of system files. Below is the list of file extensions that are encrypted. Lateral Movement. In order to spread across the network, Bad Rabbit enumerates all local subnet IP addresses and attempts to reach the following predefined SMB shares wkssvcadminatsvcbrowsereventloglsarpcnetlogonntsvcsspoolsssamrscerpcsrvsvcsvcctl. In order to authenticate to these network shares an embedded Mimikatz tool is utilized and the credentials retrieved by it is used for authentication. Additionally a predefined set of usernames and passwords are also attempted as login credentials. Usernames AdministratorAdminGuestUserUser. Testrootbuhbossftprdprdpuserrdpadminmanagersupportworkother useroperatorbackupasusftpuserftpadminnasnasusernasadminsuperusernetguestalexPasswords AdministratoradministratorGuestguestUseruserAdminadmin. Testtestrootroot1. Administrator. 12. Guest. 12. 3guest. User. 12. 3user. Admin. Test. 12. 3test. Once authenticated into a network share, the dropper will drop itself into it by copying these files sadmininfpub. These files are then remotely executed via the following WMI command c Windowssystem. C WindowsSystem. C Windowss 1Main Module. The main module contains logic for both the encryption and decryption routines. It is able to decrypt files, however it does not encrypt them since this is done in the dropper itself. Instead, this module is used to encrypt the disk after the system reboot has taken place. It interacts with a pre loaded driver for files encryption via opening this device. It then sends custom commands via Device. IOControl in order to perform different actions which include Command. Description. DCCTLLOCKMEMLock memory previously allocated by Virtual. Alloc. DCCTLCLEARPASSWipe passwords in memory. DCCTLADDSEEDAdd randomness to the generator. DCCTLENCRYPTSTARTStart of encryption routine. DCCTLENCRYPTSTEPEncryption step. It then enumerates all the system volumes while collecting the following information Mouse and keyboard hooks are then set in order to generate random values bases on mouse movements and key presses. The module retrieves the boot device by querying for Arc. Namemulti0disk0rdisk0partition1. After this the previously created scheduled tasks named rhaegal and drogon are deleted. Finally, the main module proceeds into the MBR replacement functionality in which it unpacks resources that contain a new MBR and 2nd stage loader. It then rewrites the old MBR with the new one. After which it starts the files encryption routine which is done by sending DCCTLENCRYPTSTART and DCCTLENCRYPTSTEP commands to the previously installed driver and by using the same public key used by the dropper module. Finally, the main module wipes passwords from memory with the same command request sent to the driver. It then executes shutdown.
Credentials grabber, 3. C windows. tmpmimikatz based tool. Credentials grabber, 6. C windows tmpmimikatz based tool. Main payload. C windowsdispci. Driver, 3. 2bit. C windowscscc. Legitimate signed file dcrypt. Driver, 6. 4bit. C windowscscc. Legitimate signed file dcrypt. Landscape 20050901 shutdown. Windows. The diagram below represents the overall malware flow of execution. An interactive version of this diagram can be found here. The following contains a detailed technical explanation of each of Bad Rabbit module. Dropper. The Dropper module starts its execution by unpacking and running embedded an executable, which is run via rundll. The purpose of this unpacked DLL is to perform some preparatory actions before executing the main payload and setting up the driver. Once executed, it initially checks if the directory c Windowscscc. If not then the process is terminated. It then chooses the appropriate driver from within its embedded resource 3. The driver is executed via the service manager at the time of booting. The main payload executable is then written to C windowsdispci. Following a creation of a scheduled task named rhaegal which is used to execute it on every system restart using this command line schtasks Create RU SYSTEM SC ONSTART TN rhaegal TR C WINDOWSsystem. Windows 10, like its predecessors, offers multiple ways to access shut down, restart, hibernate and sleep options in Windows 10. You can access shut down o. What is this all about Earlier this week a new ransomware attack dubbed Bad Rabbit broke out and has so far affected The Ukraine, Russia, Turkey and Bulgaria. Share Threat Hunting Services Are Now a Basic Necessity on Twitter Share Threat Hunting Services Are Now a Basic Necessity on Facebook Share Threat Hunting Services. Windows 7. Windows Server 2008 R2 Thread, GPP Deploying Scheduled Tasks SOLVED in Technical Ok so Im trying to deploy a scheduled task but having some difficulty. Files-In-System32_cmd.png' alt='C/Windows/System32/Shutdown.Exe ?' title='C/Windows/System32/Shutdown.Exe ?' />In this video I will show you how to add the shutdown, restart, sleep and logoff buttons to the taskbar. Below are the codes you will use to make the. How to Automatically Shut Down Your Computer at a Specified Time. Do you always forget to switch off your computer before going to bed, or just forget to look at the. C Start C Windowsdispci. The id argument in the above command line is set with randomly generated 4 bytes. Following the dropper module, it schedules a system shutdown by creating yet another scheduled task named drogon by using this command line. Create SC once TN drogon RU SYSTEM TR C WINDOWSsystem. ST hh mm ss. It also deletes windows events and the USN drive c journal by using this command line. Setup wevtutil cl System wevtutil cl Security wevtutil cl Application fsutil usn deletejournal D c Once these actions are complete, the dropper deletes the drogon scheduled task and starts a separate thread in order to encrypt each of the system drives. Finally, a file named Readme. A public RSA 2. 04. This keys value is E5 C9 4. B9 5. 1 6. B E6 C4 3. E7 DE 4. 2 5. 5 6. F 6. 5C1 0. A D2 4. Qual O Melhor Site Para Baixar Jogos De Xbox 360 on this page. E 2. E 0. 9 2. 1 7. A 4. 3 A4 1. 7 D0 3. B5 1. E8. E FF 1. D F3 DF CF 5. 6 1. A 3. 0 BE ED 9. 3 7. C 1. 4 D1. B2 7. 0 6. C F3 7. 8 5. C 1. F 2. 1 8. C 6. D 9. E4 5. E 4. 3 C5. 71 6. B 1. A 5. 3 A9 5. B 1. 1 E2 5. 3 A6 E4 A0 7. B C6. A9 E1 3. 8 A7 1. B F1 8. D FD 2. 5 4. D 0. 4 5. C 2. 5 9. FB D1 5. 8 D9 8. A 8. A2 1. D 4. 4 EB E4 1. F 1. C 8. 0 2. EE2 7. E0 9. 9 9. 4 8. A 1. A 2. 7 9. B 4. 1 D1 8. C 4. 1C4 C9 1. B 0. B 7. 2 7. B 5. 9 6. C7 7. 0 1. F 5. 3 FE 3. E2. 36 0. D 8. C 1. F 9. 9 5. 9 F5 B1 0. E 9. 3 B6 1. 3 3. FC 1. 5 2. 8DA AD 1. D A5 F4 2. C 9. 3 B2 0. C 7. 8 3. 5 1. D 0. C E1. 4B 0. D 0. 3 8. D 5. B D3 8. E 8. A4 4. 7 1. D D5 EC F0 B7. F 4. 7 1. E 1. C A2 2. F 2. 6 C3 9. 6 D6 5. D 6. 6 3. 6DC 0. B EC A5 FE EE 4. CD 7. B 4. 0 9. E 7. C 1. C 8. 4 5. 9 F4. B7 5. B 5. B 9. 2 F8 DD 7. FD B1 0. 6 7. 3 E3 6. F 7. 1 8. 4D4 6. 0 3. F A0 6. 7 0. 6 8. E B5 DC EB 0. 5 7. C 5. 8 AB 1. F 6. File extensions to be encrypted. Bad. Rabbit can perform both encryption and decryption of the MBR and of system files. Below is the list of file extensions that are encrypted. Lateral Movement. In order to spread across the network, Bad Rabbit enumerates all local subnet IP addresses and attempts to reach the following predefined SMB shares wkssvcadminatsvcbrowsereventloglsarpcnetlogonntsvcsspoolsssamrscerpcsrvsvcsvcctl. In order to authenticate to these network shares an embedded Mimikatz tool is utilized and the credentials retrieved by it is used for authentication. Additionally a predefined set of usernames and passwords are also attempted as login credentials. Usernames AdministratorAdminGuestUserUser. Testrootbuhbossftprdprdpuserrdpadminmanagersupportworkother useroperatorbackupasusftpuserftpadminnasnasusernasadminsuperusernetguestalexPasswords AdministratoradministratorGuestguestUseruserAdminadmin. Testtestrootroot1. Administrator. 12. Guest. 12. 3guest. User. 12. 3user. Admin. Test. 12. 3test. Once authenticated into a network share, the dropper will drop itself into it by copying these files sadmininfpub. These files are then remotely executed via the following WMI command c Windowssystem. C WindowsSystem. C Windowss 1Main Module. The main module contains logic for both the encryption and decryption routines. It is able to decrypt files, however it does not encrypt them since this is done in the dropper itself. Instead, this module is used to encrypt the disk after the system reboot has taken place. It interacts with a pre loaded driver for files encryption via opening this device. It then sends custom commands via Device. IOControl in order to perform different actions which include Command. Description. DCCTLLOCKMEMLock memory previously allocated by Virtual. Alloc. DCCTLCLEARPASSWipe passwords in memory. DCCTLADDSEEDAdd randomness to the generator. DCCTLENCRYPTSTARTStart of encryption routine. DCCTLENCRYPTSTEPEncryption step. It then enumerates all the system volumes while collecting the following information Mouse and keyboard hooks are then set in order to generate random values bases on mouse movements and key presses. The module retrieves the boot device by querying for Arc. Namemulti0disk0rdisk0partition1. After this the previously created scheduled tasks named rhaegal and drogon are deleted. Finally, the main module proceeds into the MBR replacement functionality in which it unpacks resources that contain a new MBR and 2nd stage loader. It then rewrites the old MBR with the new one. After which it starts the files encryption routine which is done by sending DCCTLENCRYPTSTART and DCCTLENCRYPTSTEP commands to the previously installed driver and by using the same public key used by the dropper module. Finally, the main module wipes passwords from memory with the same command request sent to the driver. It then executes shutdown.